All data on the internet will sooner or later change hands without owner’s knowledge. This is also the case of the user database of the second largest and oldest Tor black market. In mid October we described an incident where BMR source code was leaked due to – most probably – administrator’s error (for a brief period of time the server was displaying PHP files instead of parsing them). As it turns out user database of the service was also obtained by unauthorized party together with the source code. Thanks to one of our readers we got the unique chance to analyse it.
Database contents
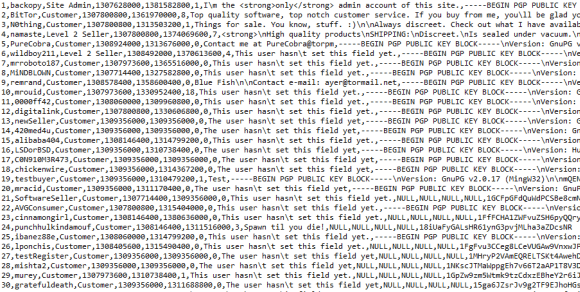
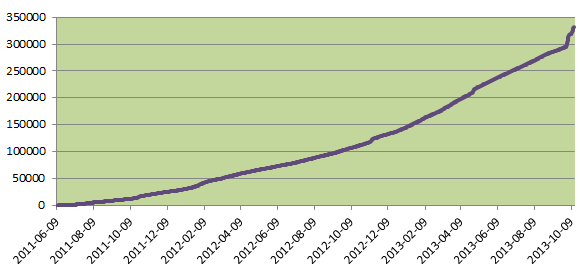
Before you start running around and screaming we need to state one important thing – the file we had an opportunity to inspect did not include user passwords in any form. It did however include the following fields: id, username, account_type, member_since, last_seen, feedback, about, gpg, gpg_name, gpg_email, gpg_time, bitcoin_addr for 332 079 accounts. The oldest account (backopy) was created on June 9, 2011 and the most recent ones are from October 14, 2013. Out of those 332k records, 12 202 contain the PGP key, 9992 contain an email address and 108 026 contain the BTC address.
We have no idea if the password hashes were stolen with the database. Backopy claims they were stored in a very complicated form, but it is possible they were leaked as well (mind the fact that 200 BTC was stolen from BMR a few days ago with no explanation).
How does it compare to Silk Road?
Is 332k users a lot? If we want to compare this number to Silk Road user base we need to look at July 23, 2013 (as FBI gave the exact SR user count for this day). SR had 957 079 users at that time, while BMR 260 800. Is the relation 1:4 relevant? We doubt so, as the financial data show a much, much bigger difference. Based on the data Backopy published we know that from February 2012 to April 2013 (15 months) the total value of transactions was around 2,85 mln USD (based on pixel count), while according to FBI SR sales amounted to 1,2 bln USD over 30 months. Assuming we can trust both Backopy and the FBI, the difference is huge.
If we look at BMR user account types, we have 323 034 customer accounts, 5692 level 1 seller accounts, 3197 level 2 seller accounts, 152 accounts marked as „scammer”, 3 support team accounts (LeContog, Ilovespaghetti, sh4d3r1950) and of course 1 administrator account – backopy.
Silk Road influence
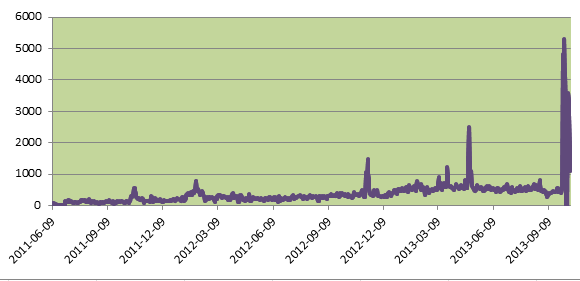
During the 859 days covered in the database over 332k users registered on BMR. But how was this process distributed over time? It looks like it was largely influenced by Silk Road accessibility.
The first anomaly took place around October 20-26 2011. Based on Silk Road forum entries we can confirm that at this period of time SR suffered technical problems and was rarely accessible. BMR daily registrations grew from regular 100-200 to 300-600.
Next sudden growth took place end of January / beginning of February 2012. Instead of 300-400 daily new users BMR saw 500-800. Again this correlates to SR accessibility problems.
Next big anomaly happens between November 9 and 14 2012 when BMR sees 5,5k new users during 5 days. Again this is a period of time, when SR was hardly accessible due to infrastructure problems and scalability.
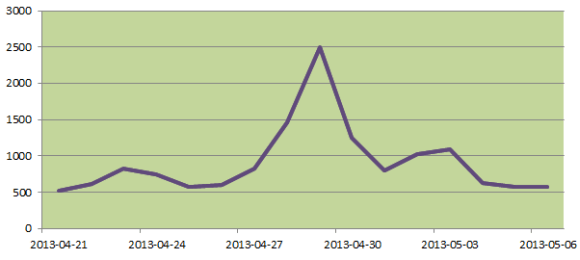
One of the largest growth periods in BMR history took place end of April / beginning of May 2013 (9k new users in one week), which in turn was caused by SR being under heave DDoS attacks.
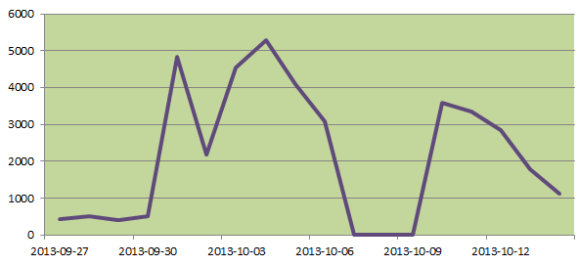
The last big jump is obvious and is related to FBI closing SR. As you can see on the graph below BMR was overwhelmed by new customers and vendors. Daily registrations increased 10-fold and stayed that way until 7 days later BMR turned of registrations for 3 days. When it came back it saw again a few thousands new users a day.
What is also an interesting observation is total lack of any influence of closing Atlantis at the end of September. It had aboslutely no visible impact on the number of new user registrations on BMR.
Users activity
We know that BMR had plenty of users, but how many of them were really active? It is not an easy question without the transaction register, but we can try to estimate it based on the available data. In October over 51k users visited the website at least once, while 37k out of those 51k registered their accounts in October. This leads to 14k users, who had an account before they visited in October.
Other measure shows that 226k users registered and visited the website for the last time on the same day, so in most cases it was their first and only visit. Additional 19k visited the website the next day after they registered and never did it again. So we have around 87k users who registered on the website and visited it at least two days later. Those two approaches help to estimate the number of active users somewhere between 14k and 87k.
Ten best vendors
The database contains also information about user reputation. When sorted by highest reputation, the 10 users below show on top. Position 9 is interesting, showing vendor TooLegit with lots of reputation point and a „scammer” status – looks like he pulled a „Tony76”.
1394,CaliBud2012,Level 2 Seller 1391,fake,Level 2 Seller 1145,kukkaavaan,Level 2 Seller 801,demonfifa,Level 1 Seller 660,Prodige,Level 2 Seller 630,valid_CC_info,Level 1 Seller 540,omx,Level 2 Seller 532,moramaru,Level 2 Seller 462,TooLegit,SCAMMER 455,Apteekki,Level 2 Seller
Summary
Because of the contents of the database and lack of user passwords the data has more value for researchers that for blackhats. However we can’t confirm or deny if the password hashes were also obtained by the opportunistic hacker. So if you – for research reasons only – had an account on BMR we recommend to change your password as soon as the market comes back online.